Would it be possible to add slow hash encryption options (like PBKDF2 or bcrypt) to Wappler?
I ask because I wasn't sure which of Wappler's default cryptographic options I should use to encrypt user passwords for my web app. So I did some googling and the recommended options seem to be PBKDF2, bcrypt or scrypt.
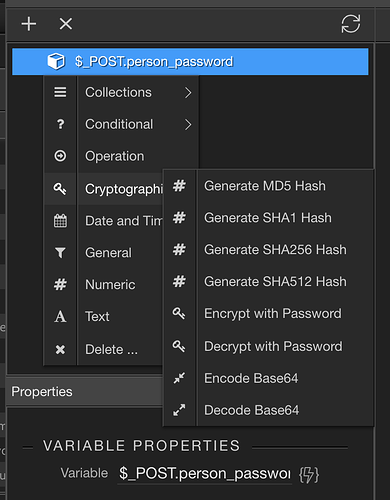
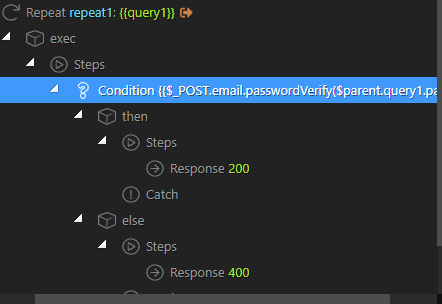
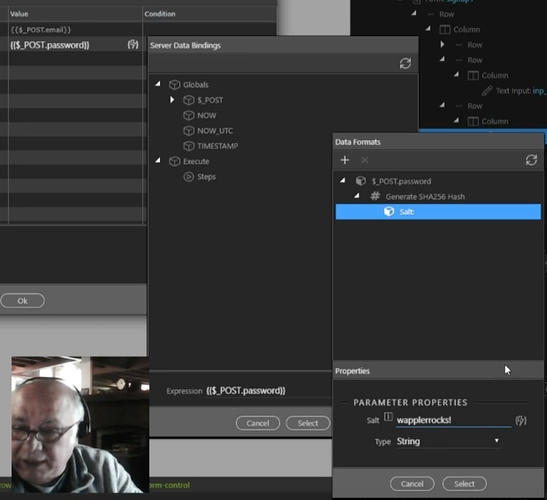
From what I can tell, Wappler doesn't offer any of these. Here is a screenshot of Wappler's current cryptographic options...
This security article is somewhat dated (from 2013), but it's general conclusion is...
Passwords should be hashed with either PBKDF2, bcrypt or scrypt. MD-5 and SHA-3 should never be used for password hashing and SHA-1/2(password+salt) are a big no-no as well. Currently the most vetted hashing algorithm providing most security is bcrypt. PBKDF2 isn’t bad either, but if you can use bcrypt you should. Scrypt, while still considered very secure, hasn’t been around for a long time, so it doesn’t get recommended a lot, but it seems it will become the successor of bcrypt, once it has been around a bit longer. Note that while there are some caveats and password bruteforcing strategies for PBKDF2 and bcrypt, they are still considered unfeasable for strong passwords (passwords longer than 8 characters, containing numbers, letters, signs and at least one capital letter).
A somewhat more recent security article (from 2016) says...
... it is not recommended that regular web applications use any member of the SHA family, be it SHA1, SHA256, or even SHA512 for password hashing. The reason is that all of these hashes are fast hashes . When an attacker gets access to your database of password hashes and he also has a copy of your salt, which he presumably will considering that your server was compromised, then your users’ passwords are in danger. With a fast hash, the attacker can compute billions of hashes per second in an offline attack.
I read a handful of other articles too and the general thinking seems to be that fast hashes (like the SHA family) are less secure and not recommended, while slow hashes (like PBKDF2, bcrypt and scrypt) are recommended. The Laravel and Rails frameworks uses bcrypt I believe. There is a PHP implementation of PBKDF2.
This detailed 2019 security article also recommends slow hashes.
I am not a security expert so if I'm misunderstanding the current Wappler cryptographic options, please let me know.
Much appreciated!