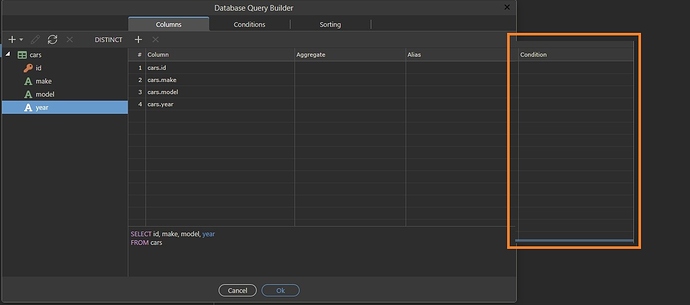
Perhaps I did not correctly explain why I want to use the conditions in the db query builder?
I’ll try to give an example. Imagine that we have three roles in the system. And each role has a different set of rights relative to this table:
Role 1 - should only see the id and make fields
Role 2 - can see the id, make and model fields
Role 3 - sees the data of all fields
And when I say data restriction, I’m talking about getting this data in a client-side request.
In order to implement this functionality now, I need to do such a server action, in which first there is a determination of what role the user has, and then, depending on the role, one of three different database queries will be used. In fact, you need to create three different server actions. At the same time, all roles must be defined in advance, and their rights are rigidly fixed in server actions.
In the event that the requested functionality is implemented in the Wappler, you would not have to create different server actions. It would be enough to have one server action that can serve requests from any number of roles. The role check could be included in the condition for each column. Therefore, the request would have all 4 fields, but in each field there was a check whether the user belongs to a role that can have access to the field. This would result in the same server action returning a different amount of data, depending on which user made the request to the table. It’s very convenient and very flexible!
With this functionality, you can create systems in which administrators themselves can create any number of roles, and configure access to data for each field for each role.
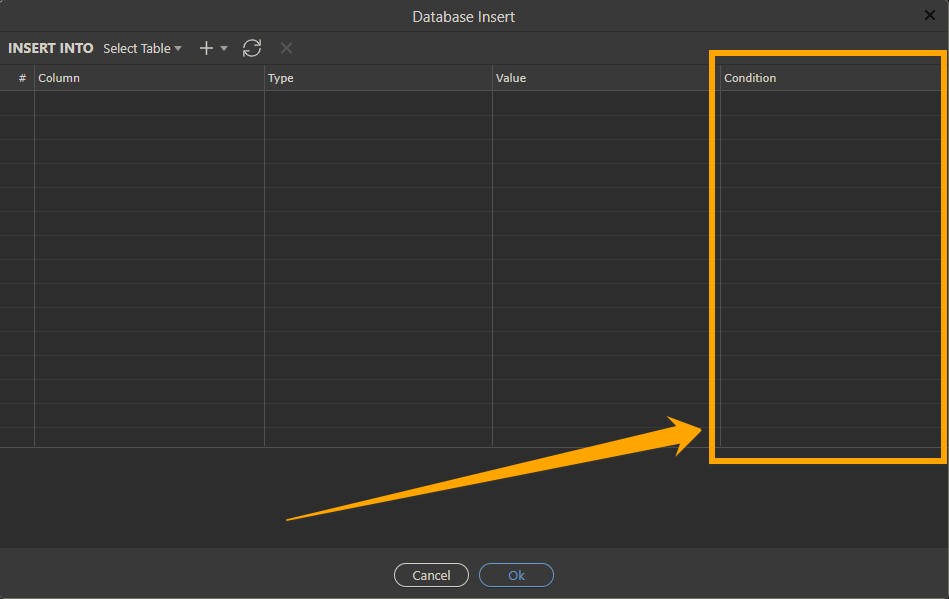
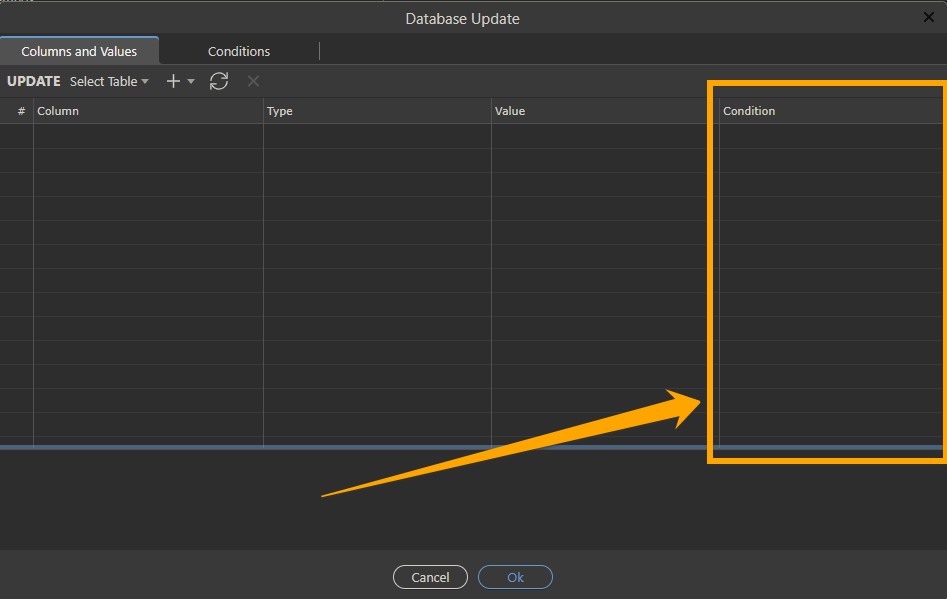
The current implementation of the database query builder in the Wappler does not allow creating such a security system in the application, because conditions cannot be created and all requests are static.